The newly updated Cisco 200-201 dumps contain 264 exam questions and answers that candidates can study using the 200-201 dumps PDF and 200-201 dumps VCE to help you successfully pass the 200-201 CBROPS exam.
You are welcome to download the latest Cisco 200-201 dumps: https://www.leads4pass.com/200-201.html, leads4pass 200-201 dumps serve all candidates taking the 200-201 CBROPS exam and guarantee you 100% Successfully passed the 200-201 CBROPS exam.
Download the Cisco 200-201 PDF for free sharing online:
https://drive.google.com/file/d/1NvgnmVOH2wzbAtjRlNnpN57M70GgdSeW/
https://drive.google.com/file/d/1Hq9tXhs7kyJzL3cTTXNNYoTOKZOld2X7/
Share the latest Cisco 200-201 dumps exam questions and answers for free
New Question 1:
Refer to the exhibit.
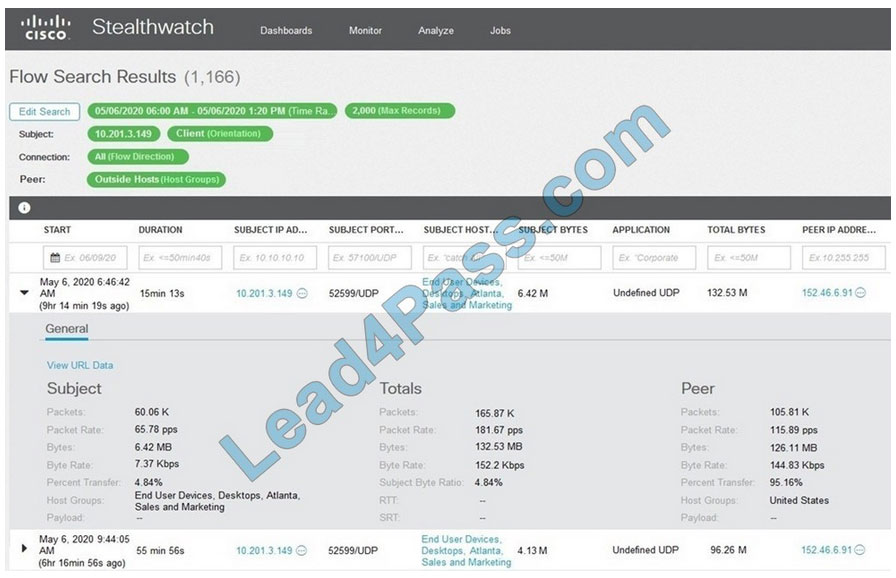
What is the potential threat identified in this Stealthwatch dashboard?
A. Host 10.201.3.149 is sending data to 152.46.6.91 using TCP/443.
B. Host 152.46.6.91 is being identified as a watchlist country for data transfer.
C. Traffic to 152.46.6.149 is being denied by an Advanced Network Control policy.
D. Host 10.201.3.149 is receiving almost 19 times more data than is being sent to host 152.46.6.91.
Correct Answer: D
New Question 2:
What does cyber attribution identify in an investigation?
A. cause of an attack
B. exploit of an attack
C. vulnerabilities exploited
D. threat actors of an attack
Correct Answer: D
New Question 3:
Refer to the exhibit.
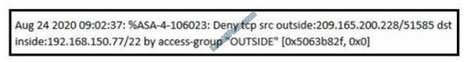
An analyst received this alert from the Cisco ASA device, and numerous activity logs were produced. How should this type of evidence be categorized?
A. indirect
B. circumstantial
C. corroborative
D. best
Correct Answer: C
Indirect=circumstantail so there is no possibility to match A or B (only one answer is needed in this question). For sure it\’s not the BEST evidence – this FW data inform only of DROPPED traffic. If smth happened inside the network, presented evidence could be used to support other evidence or make our narration stronger but alone it\’s means nothing.
New Question 4:
What is a sandbox interprocess communication service?
A. A collection of rules within the sandbox that prevent communication between sandboxes.
B. A collection of network services that are activated on an interface, allowing for inter-port communication.
C. A collection of interfaces that allow for coordination of activities among processes.
D. A collection of host services that allow for communication between sandboxes.
Correct Answer: C
Inter-process communication (IPC) allows communication between different processes. A process is one or more threads running inside its own, isolated address space.
New Question 5:
A security specialist notices 100 HTTP GET and POST requests for multiple pages on the web servers. The agent in the requests contains PHP code that, if executed, creates and writes to a new PHP file on the web server. Which event category is described?
A. reconnaissance
B. action on objectives
C. installation
D. exploitation
Correct Answer: C
New Question 6:
What is the practice of giving an employee access to only the resources needed to accomplish their job?
A. principle of least privilege
B. organizational separation
C. separation of duties
D. need to know the principle
Correct Answer: A
New Question 7:
Refer to the exhibit.
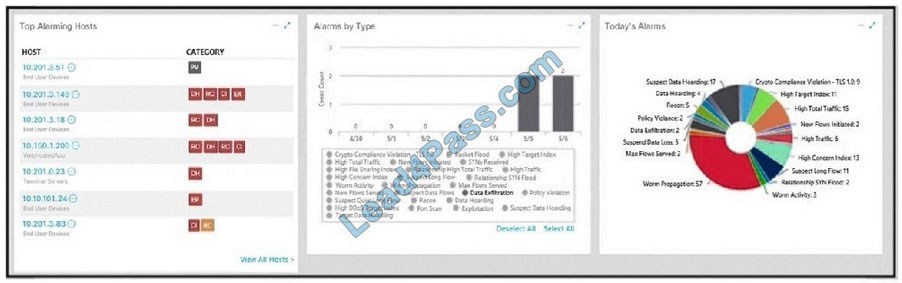
What is the potential threat identified in this Stealthwatch dashboard?
A. A policy violation is active for host 10.10.101.24.
B. A host on the network is sending a DDoS attack to another inside host.
C. There are two active data exfiltration alerts.
D. A policy violation is active for host 10.201.3.149.
Correct Answer: C
New Question 8:
Which incidence response step includes identifying all hosts affected by an attack?
A. detection and analysis
B. post-incident activity
C. preparation
D. containment, eradication, and recovery
Correct Answer: D
3.3.3 Identifying the Attacking Hosts During incident handling, system owners and others sometimes want to or need to identify the attacking host or hosts. Although this information can be important, incident handlers should generally stay focused on containment, eradication, and recovery. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
The response phase, or containment, of incident response, is the point at which the incident response team begins interacting with affected systems and attempts to keep further damage from occurring as a result of the incident.
New Question 9:
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?
A. availability
B. confidentiality
C. scope
D. integrity
Correct Answer: D
New Question 10:
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
A. MAC is controlled by the discretion of the owner and DAC is controlled by an administrator
B. MAC is the strictest of all levels of control and DAC is object-based access
C. DAC is controlled by the operating system and MAC is controlled by an administrator
D. DAC is the strictest of all levels of control and MAC is object-based access
Correct Answer: B
New Question 10:
What is vulnerability management?
A. A security practice focused on clarifying and narrowing intrusion points.
B. A security practice of performing actions rather than acknowledging the threats.
C. A process to identify and remediate existing weaknesses.
D. A process to recover from service interruptions and restore business-critical applications
Correct Answer: C
Reference: https://www.brinqa.com/vulnerability-management-primer-part-2-challenges/ Vulnerability management is the “cyclical practice of identifying, classifying, prioritizing, remediating and mitigating” software vulnerabilities.[1] Vulnerability management is integral to computer security and network security, and must not be confused with Vulnerability assessment” source: https://en.wikipedia.org/wiki/Vulnerability_management
New Question 12:
Which type of evidence supports a theory or an assumption that results from initial evidence?
A. probabilistic
B. indirect
C. best
D. corroborative
Correct Answer: D
Corroborating evidence (or corroboration) is evidence that tends to support a theory or an assumption deduced by some initial evidence. This corroborating evidence confirms the proposition. Cisco CyberOps Associate CBROPS 200-201 Official Cert Guide
New Question 13:
What is the difference between deep packet inspection and stateful inspection?
A. Deep packet inspection gives insights up to Layer 7, and stateful inspection gives insights only up to Layer 4.
B. Deep packet inspection is more secure due to its complex signatures, and stateful inspection requires less human intervention.
C. Stateful inspection is more secure due to its complex signatures, and deep packet inspection requires less human intervention.
D. Stateful inspection verifies data at the transport layer and deep packet inspection verifies data at the application layer
Correct Answer: B
New Question 14:
A company encountered a breach on its web servers using IIS 7 5 Dunng the investigation, an engineer discovered that an attacker read and altered the data on a secure communication using TLS 1 2 and intercepted sensitive information by downgrading a connection to export-grade cryptography. The engineer must mitigate similar incidents in the future and ensure that clients and servers always negotiate with the most secure protocol versions and cryptographic parameters. Which action does the engineer recommend?
A. Upgrade to TLS v1 3.
B. Install the latest IIS version.
C. Downgrade to TLS 1.1.
D. Deploy an intrusion detection system
Correct Answer: B
New Question 15:
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
A. examination
B. investigation
C. collection
D. reporting
Correct Answer: C
…
Download the Cisco 200-201 PDF for free sharing online:
https://drive.google.com/file/d/1NvgnmVOH2wzbAtjRlNnpN57M70GgdSeW/
https://drive.google.com/file/d/1Hq9tXhs7kyJzL3cTTXNNYoTOKZOld2X7/
The above is only a part of Cisco 200-201 dumps exam questions and answers, you can use the above exam questions and answers to improve yourself, not only that, we welcome you to download the latest
Cisco 200-201 dumps exam questions: https://www.leads4pass.com/200-201.html (Total Questions: 264 Q&A), help you truly pass the 200-201 CBROPS exam.
More IT certification blogs: [Amazon]awsexamdumps.com, [Oracle]oraclefreedumps.com, [Cisco]ciscofreedumps.com, [Microsoft]examdumpsbase.com, [Citrix]citrixexamdumps.com
[CompTIA]comptiafreedumps.com, [VMware]vmwarefreedumps.com, [IBM]ibmexamdumps.com, [HP]hpexamdumps.com, [NetApp]netappexamdumps.com, [Juniper]juniperexamdumps.com
[Fortinet]fortinetexamdumps.com