CyberOps Professional 350-201 Dumps is the Cisco CBRCOR exam material for core cybersecurity operations. leads4pass 350-201 Dumps Prepares Candidates for Cisco CBRCOR Exam Questions and Answers https://www.leads4pass.com/350-201.html helps you earn the Cisco CyberOps Professional Core Certification.
Cisco technology is spread all over the world. This means that CyberOps Professional certified professionals will continue to be sought after, as long as you ensure that you can successfully achieve the CyberOps Professional 350-201 certification. Use the CyberOps Professional 350-201 dumps to guarantee your success with the Cisco CyberOps Professional Core certification.
CyberOps Professional Core FAQs: About, Value, Exam Material
About 350-201 CBRCOR: What You Need to Know
Vendor: Cisco
Exam Code: 350-201
Exam Name: Performing CyberOps Using Cisco Security Technologies (CBRCOR)
Certification: CyberOps Professional
Languages: English
Price: $400 USD
Duration: 120 mins
Number of Questions: 90-110 questions
Passing score: 80% Approx
350-201 dumps: https://www.leads4pass.com/350-201.html (CyberOps Professional core exam dumps maps to Cisco 350-201 CBRCOR exam objectives))
350-201 dumps (Number of Questions): 139 Q&A
Last update time: Sep 23, 2022
Is CyberOps Professional Core certification worth it?
As the complexity of cyberattacks continues to increase in size and scale, your organization needs highly qualified personnel to provide security expertise before, during, and after an attack. The demand is greater now than ever before for professionals with the knowledge and skills to detect and respond to cybersecurity threats, manage security incidents, automate security tasks, and secure the sensitive information of your organization.
Achieving the Cisco Certified CyberOps Professional certification proves your advanced skills as a senior analyst, in a security operation center (SOC), incident response, cloud security, and other active defense security roles.
Free share of a portion of the CyberOps Professional 350-201 CBRCOR exam material
| Number of exam questions | Exam name | From | Release time |
| 15 | Performing CyberOps Using Cisco Security Technologies (CBRCOR) | leads4pass | Sep 30, 2022 |
New Question 1:
Refer to the exhibit. A threat actor behind a single computer exploited a cloud-based application by sending multiple concurrent API requests. These requests made the application unresponsive. Which solution protects the application from being overloaded and ensures more equitable application access across the end-user community?
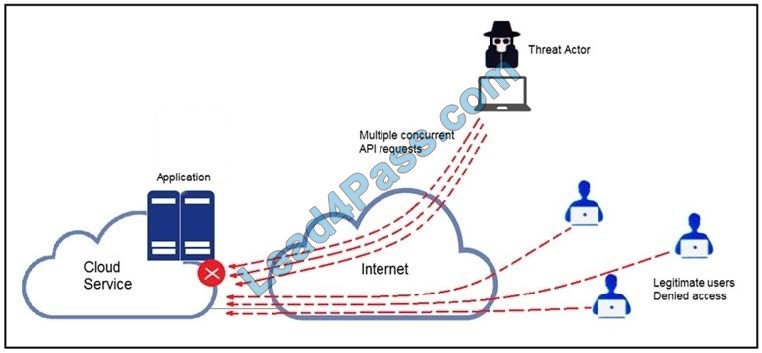
A. Limit the number of API calls that a single client is allowed to make
B. Add restrictions on the edge router on how often a single client can access the API
C. Reduce the amount of data that can be fetched from the total pool of active clients that call the API
D. Increase the application cache of the total pool of active clients that call the API
Correct Answer: A
New Question 2:
A threat actor attacked an organization\’s Active Directory server from a remote location, and in a thirty-minute timeframe, stole the password for the administrator account and attempted to access 3 company servers. The threat actor successfully accessed the first server that contained sales data, but no files were downloaded. A second server was also accessed that contained marketing information and 11 files were downloaded. When the threat actor accessed the third server that contained corporate financial data, the session was disconnected, and the administrator\’s account was disabled.
Which activity triggered the behavior analytics tool?
A. accessing the Active Directory server
B. accessing the server with financial data
C. accessing multiple servers
D. downloading more than 10 files
Correct Answer: C
New Question 3:
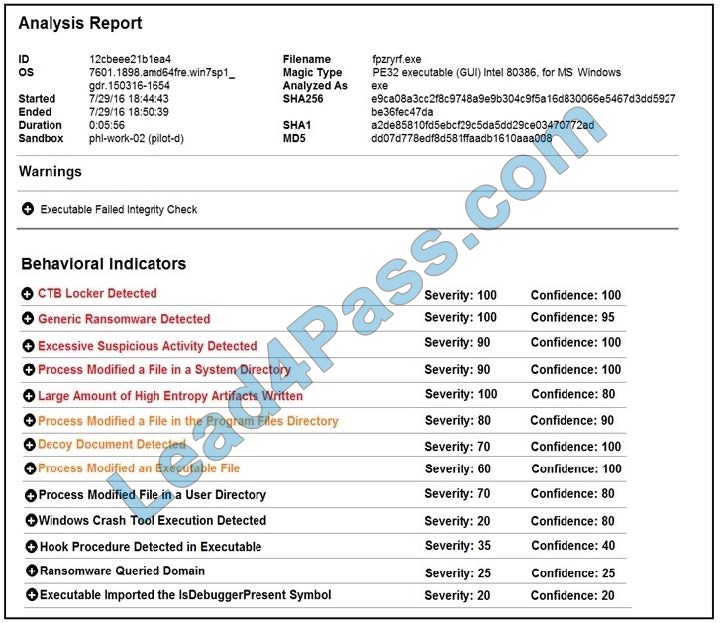
Refer to the exhibit. Cisco Advanced Malware Protection installed on an end-user desktop has automatically submitted a low prevalence file to the Threat Grid analysis engine for further analysis. What should be concluded from this report?
A. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores do not indicate the likelihood of malicious ransomware.
B. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores are high and do not indicate the likelihood of malicious ransomware.
C. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are high and indicate the likelihood that malicious ransomware has been detected.
D. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are low and indicate the likelihood that malicious ransomware has been detected.
Correct Answer: C
New Question 4:
The physical security department received a report that an unauthorized person followed an authorized individual to enter a secured premises. The incident was documented and given to a security specialist to analyze. Which step should be taken at this stage?
A. Determine the assets to which the attacker has access
B. Identify assets the attacker handled or acquired
C. Change access controls to high-risk assets in the enterprise
D. Identify the movement of the attacker in the enterprise
Correct Answer: D
New Question 5:
A new malware variant is discovered hidden in pirated software that is distributed on the Internet. Executives have asked for an organizational risk assessment. The security officer is given a list of all assets. According to NIST, which two elements are missing to calculate the risk assessment? (Choose two.)
A. incident response playbooks
B. asset vulnerability assessment
C. report on staff members with asset relations
D. key assets and executives
E. malware analysis report
Correct Answer: BE
Reference: https://cloudogre.com/risk-assessment/
New Question 6:
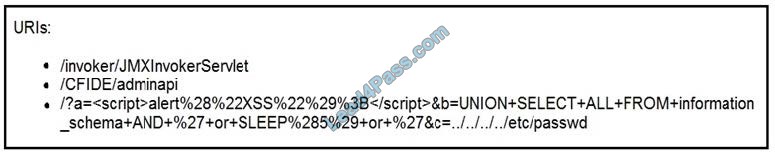
Refer to the exhibit. At which stage of the threat kill chain is an attacker, based on these URIs of inbound web requests from known malicious Internet scanners?
A. exploitation
B. actions on objectives
C. delivery
D. reconnaissance
Correct Answer: C
Reference: https://www2.deloitte.com/content/dam/Deloitte/sg/Documents/risk/sea-risk-cyber-101-july2017.pdf
New Question 7:
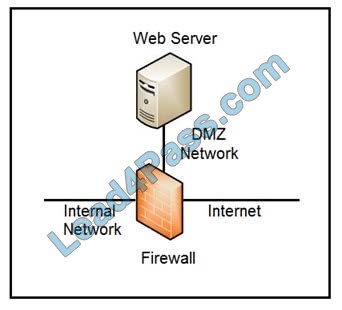
Refer to the exhibit. Which two steps mitigate attacks on the webserver from the Internet? (Choose two.)
A. Create an ACL on the firewall to allow only TLS 1.3
B. Implement a proxy server in the DMZ network
C. Create an ACL on the firewall to allow only external connections
D. Move the webserver to the internal network
Correct Answer: BD
New Question 8:
According to GDPR, what should be done with data to ensure its confidentiality, integrity, and availability?
A. Perform a vulnerability assessment
B. Conduct a data protection impact assessment
C. Conduct penetration testing
D. Perform awareness testing
Correct Answer: B
New Question 9:
A payroll administrator noticed unexpected changes within a piece of software and reported the incident to the incident response team. Which actions should be taken at this step in the incident response workflow?
A. Classify the criticality of the information, research the attacker\’s motives, and identify missing patches
B. Determine the damage to the business, extract reports, and save evidence according to a chain of custody
C. Classify the attack vector, understand the scope of the event, and identify the vulnerabilities being exploited
D. Determine the attack surface, evaluate the risks involved, and communicate the incident according to the escalation plan
Correct Answer: B
New Question 10:
A company recently completed an internal audit and discovered that there is a CSRF vulnerability in 20 of its hosted applications. Based on the audit, which recommendation should an engineer make for patching?
A. Identify the business applications running on the assets
B. Update software to patch third-party software
C. Validate CSRF by executing exploits within Metasploit
D. Fix applications according to the risk scores
Correct Answer: D
New Question 11:
An engineer is analyzing a possible compromise that happened a week ago when the company? (Choose two.)
A. firewall
B. Wireshark
C. autopsy
D. SHA512
E. IPS
Correct Answer: AB
New Question 12:
An organization had a breach due to a phishing attack. An engineer leads a team through the recovery phase of the incident response process. Which action should be taken during this phase?
A. Host a discovery meeting and define configuration and policy updates
B. Update the IDS/IPS signatures and reimage the affected hosts
C. Identify the systems that have been affected and tools used to detect the attack
D. Identify the traffic with data capture using Wireshark and review email filters
Correct Answer: C
New Question 13:
An engineer is going through vulnerability triage with company management because of a recent malware outbreak from which 21 affected assets need to be patched or remediated. Management decides not to prioritize fixing the assets and accepts the vulnerabilities.
What is the next step the engineer should take?
A. Investigate the vulnerability to prevent further spread
B. Acknowledge the vulnerabilities and document the risk
C. Apply vendor patches or available hotfixes
D. Isolate the assets affected in a separate network
Correct Answer: D
New Question 14:
The incident response team receives information about the abnormal behavior of a host. A malicious file is found being executed from an external USB flash drive. The team collects and documents all the necessary evidence from the computing resource.
What is the next step?
A. Conduct a risk assessment of systems and applications
B. Isolate the infected host from the rest of the subnet
C. Install malware prevention software on the host
D. Analyze network traffic on the host\’s subnet
Correct Answer: B
New Question 15:
An organization had several attacks over the last 6 months and has tasked an engineer with looking for patterns or trends that will help the organization anticipate future attacks and mitigate them. Which data analytic technique should the engineer use to accomplish this task?
A. diagnostic
B. qualitative
C. predictive
D. statistical
Correct Answer: C
…
[Free Download] CyberOps Professional 350-201 CBRCOR exam material:
https://drive.google.com/file/d/1fVobEt59xzJeVskbkEVtYqiUvvYE3-Xn/
https://drive.google.com/file/d/1AWESvo5Beac9z16xeX9pw-cyNhDM0Cnc/
The above are free to share 15 350-201 CBRCOR exam material, click here to get more exam questions and answers.